Troubleshooting Event ID 680 sometimes gets really tricky and I haven’t came across a good article which has described the process on how to start.
Many a times users account will keep on getting locked-out, there are few possibilities for this, like:
1. User save domain account username and password, and when the password is changed the saved credentials are not updated, the application which is using saved credentials is still sending the old password for authentication, but domain controller says I don’t have this credentials and the account lock-out.
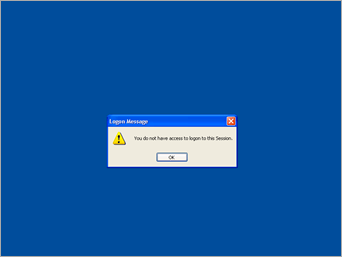
2. User (IT admin) logs on the server via RDC and forgets to logoff. There are group policy (not sure which one, will update on this later) to logoff the user session after specified time period. In case if the GPO is not in place and the connect is disconnected instead of logging Off, and again the password change occurs, the account keeps locking out.
3. The scenario which I will document in this article is related to “Logon As” account for services.
Lets check what exactly is happening here.
Event Type: Failure Audit
Event Source: Security
Event Category: Account Logon
Event ID: 680
Date: 10/31/2012
Time: 9:52:59 AM
User: NT AUTHORITY\SYSTEM
Computer: HQDC1
Description:
Logon attempt by: MICROSOFT_AUTHENTICATION_PACKAGE_V1_0
Logon account: nadeem
Source Workstation:
Error Code: 0xC0000064
The Error Code mentioned in Description says, “User name does not exist” Refer (http://www.ultimatewindowssecurity.com/securitylog/encyclopedia/event.aspx?eventid=680)
The user account is nadeem. (one of the admin who was responsible for server hardware health check).
Source Workstation is Blank!!.. now how to track this event, from where the authentication is taking place?
To start troubleshooting we will 1st enabled the Logging of “NetLogon” service.
Logging has to be enabled on Domain Controller on which the event is getting logged, as the authentication is taking place on DC.
To enable Logging, go to command prompt and run:
nltest /dbflag:0x20000004
And restart “NetLogon” service
net stop netlogon
net start netlogon
Now, go to the location “C:\windows\Debug”
Here you will find “NetLogon.log” file, this is where the logging will recorded.
You can see in the log file, we can see the user authentication request is coming from a server named “HQANTIVIRUS” 
So, we got the source server and its time to logon to the server and check it.
TIP: as soon as you logon check “Processes”tab under “Windows task manager” and find the Username along with the corresponding executable which is issuing authentication request
In this case, what I found was “hpsimsvc.exe” was showing username as “nadeem”
Next, I check the services.msc and found out the service is Logged on as “nadeem” 
Once, you fix this, the event will not show up ![]() .
.
Let us disable the logging of NetLogon.
From command prompt run:
nltest /dbflag:0x0
And restart “NetLogon” service
net stop netlogon
net start netlogon